Why Use Mobile Endpoint Security To Safeguard Your Mobile Devices
Mobile devices have become indispensable tools in our daily lives, serving as portals to a wealth of information and resources. However, the increasing reliance on smartphones and tablets has also made them prime targets for cyber threats. Mobile endpoint security solutions play a crucial role in protecting these devices and the sensitive data they contain from a multitude of threats, ranging from malware and phishing attacks to device theft and data breaches.
The importance of mobile endpoint security:
As mobile devices store a treasure trove of personal and sensitive information, including emails, contacts, photos, and financial data, they have become lucrative targets for cybercriminals. Mobile endpoint security aims to mitigate these risks by implementing measures to detect, prevent, and respond to various threats that may compromise the security and privacy of mobile devices and their users.
Key features of mobile endpoint security solutions:
Mobile device management (MDM): MDM solutions enable organizations to remotely manage and secure mobile devices within their networks. This includes features such as device encryption, remote wipe, and policy enforcement to ensure compliance with security standards and regulations.
Mobile application management (MAM): MAM solutions focus on securing and managing mobile applications installed on devices. This involves app whitelisting, blacklisting, and containerization to prevent the installation of malicious apps and protect sensitive corporate data.
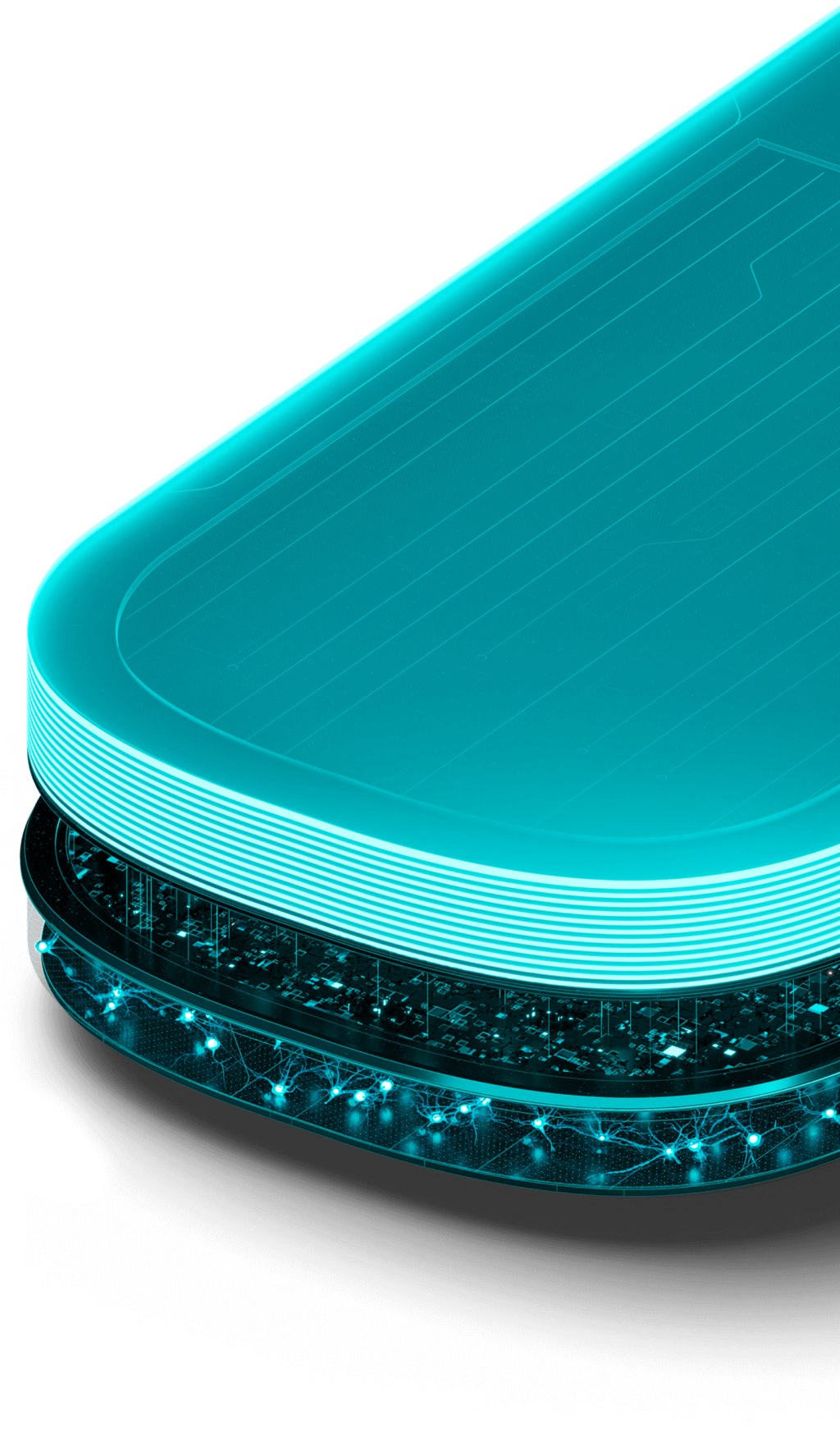
Mobile threat defense (MTD): MTD solutions use advanced threat detection techniques to identify and mitigate mobile-specific threats, including malware, phishing, and network attacks. These solutions often leverage machine learning and behavioral analysis to detect anomalous behavior indicative of malicious activity.
Endpoint detection and response (EDR): EDR solutions extend endpoint security capabilities to mobile devices, enabling real-time threat detection, investigation, and response. This includes monitoring for suspicious activities, such as unauthorized access attempts and data exfiltration, to prevent security incidents and breaches.
Top mobile endpoint security solutions:
Lookout: Lookout offers a complete mobile endpoint security platform designed to protect devices, data, and users from a wide range of threats. Its features include mobile threat detection, app risk assessment, and device management capabilities, making it a popular choice for organizations seeking robust mobile security solutions.
MobileIron: MobileIron provides an integrated endpoint management and security platform tailored for mobile devices. Its suite of solutions includes MDM, MAM, and threat defense capabilities to secure devices, apps, and data across diverse mobile environments.




